Part 1 – Deploying Microsoft Intune PFX connector in an Enterprise world…common practices
Last year I had the change to implement PFX certificate infrastructure for a large enterprise customer. Occasion of the project was a migration of Citrix XenMobile (XDM) to Microsoft Intune as strategic mobile device- and application management solution.

In a series of blogposts I’m sharing my experiences, design decisions, common practices and challenges of implementing Microsoft Intune PFX connector as certificate deployment mechanism in an enterprise environment.
- Part 1 – Deploying Microsoft Intune PFX connector in an Enterprise world: common practices
- Part 2 – Deploying Microsoft Intune PFX connector in an Enterprise world: troubleshooting
One of the main challenges was providing the same level (IST) of security controls but preferably the proposed solution has to provide a higher level of security (SOLL). Another complicating factor was an organization merge to a single infrastructure while maintaining functionality during migration, as a big-bang migration was no option. In this blog I’ll not go into details of the migration itself (although this topic might a blog worthwhile).
As the default Microsoft Conditional Access (CA) didn’t provide the full desired functionality, protecting on premise resources including and securely unlocking line of business apps and access to corporate Wi-Fi network. During the design phase we were considering multiple options and facing ditto challenges with pros and cons. Our best fit, given the architectural design principal and available technology was Certificate Based Authentication (CBA). Using CBA provided us a single solution which fulfills most of our requirements in relative ease way with respect to the current infrastructure.
- Providing secure (conditional) access to e-mail based on Microsoft Exchange on premise;
- Providing secure access to corporate (back-end) resources using auto-VPN;
- Seamless experience of connecting to secure corporate Wi-Fi networks;
- Access to all corporate resources blocked/revoked in a single action.
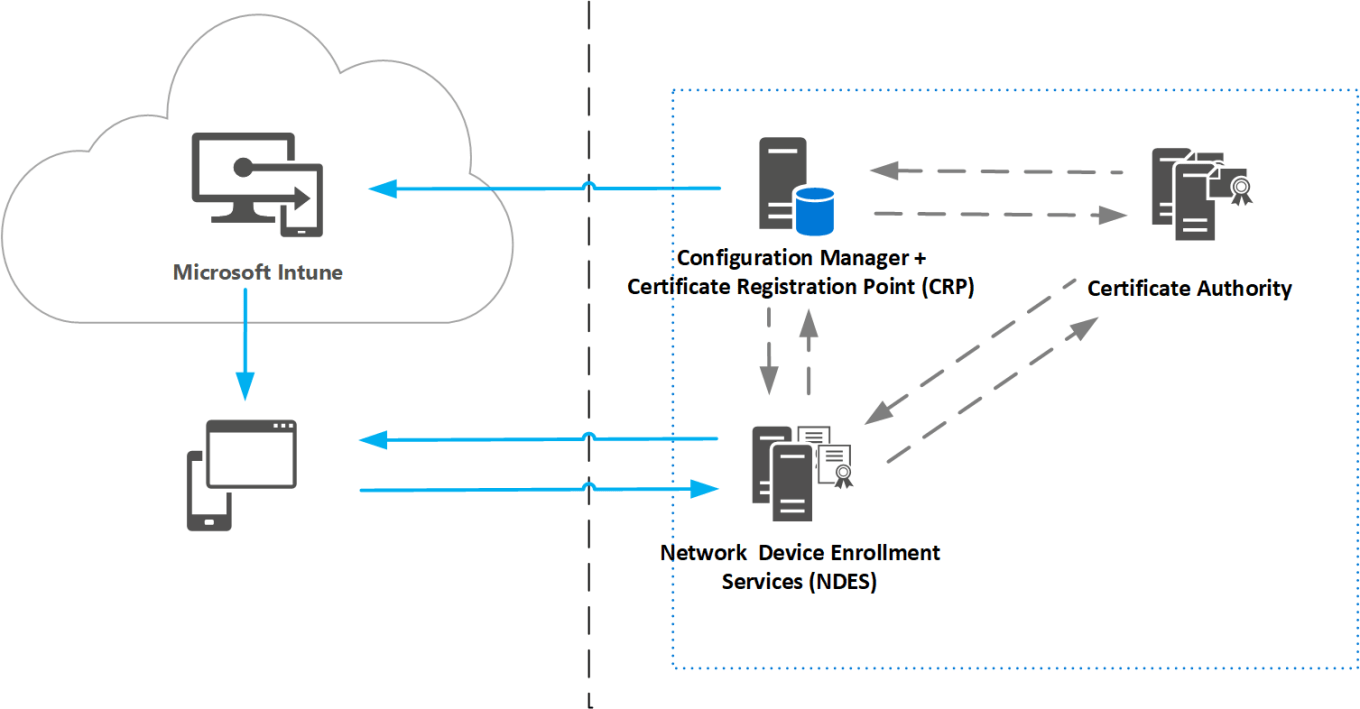
As we implemented Microsoft Intune in a standalone (cloud only) scenario we had the option to implement a certificate infrastructure to deploy user certificates to devices by using the Intune Certificate connector. The Intune Certificate connector offers two options to deploy certificates :
- Certificate infrastructure based on SCEP (Simple Certificate Enrollment Protocol)
- Certificate infrastructure based on PFX (Personal Information Exchange) aka PKCS12* (Public Key Cryptographic Standards)
*https://en.wikipedia.org/wiki/PKCS
Simple Certificate Enrollment Protocol (SCEP)
- Mobile device generates the private/public key pair;
- Unlike PFX method, the private key never leaves the device;
- Unique key and certificate on every device allows certificate revocation for just a specific device;
- Has larger infrastructure footprint compared to PFX (complex);
- Supports Windows Hello for Business certificate based scenario.
| Challenge | Solution |
| An old protocol designed for closed networks. Does not strongly authenticate certificate requests | Intune and Configuration Manager integrates closely with Network Device Enrollment Service (part of Active Directory Certificate Services) to provide higher security of certificate requests |
| Private keys can be exported from client devices | Devices must be rooted or jail broken, and Intune can detect these devices. Certificates for Windows and Windows Mobile can be protected by TPM |
Personal Information Exchange (PFX)
- MDM servers generates private key and certificate and deploys it to the mobile device.
- Entire certificate is self-contained and can be issued on behalf of the user and stored in Intune’s KRA (Key Recovery Agent)
- The same certificate can be distributed to multiple devices of the same user. Thus, provides S/MIME support for email encryption and digital signatures
- Has smaller infrastructure footprint compared to SCEP (simplified).
| Challenge | Solution |
| How does Intune secure PFX files | The PFX file is always encrypted by Intune’s KRA certificate and the device management certificate to which it is targeted |
The solution
We decided to implement certificate infrastructure based on PFX to deploy user certificates and allows us to achieve the requirements mentioned above including certificate based authentication (CBA) which allows us to access various applications like e-mail-, VPN-, Wi-Fi profiles.
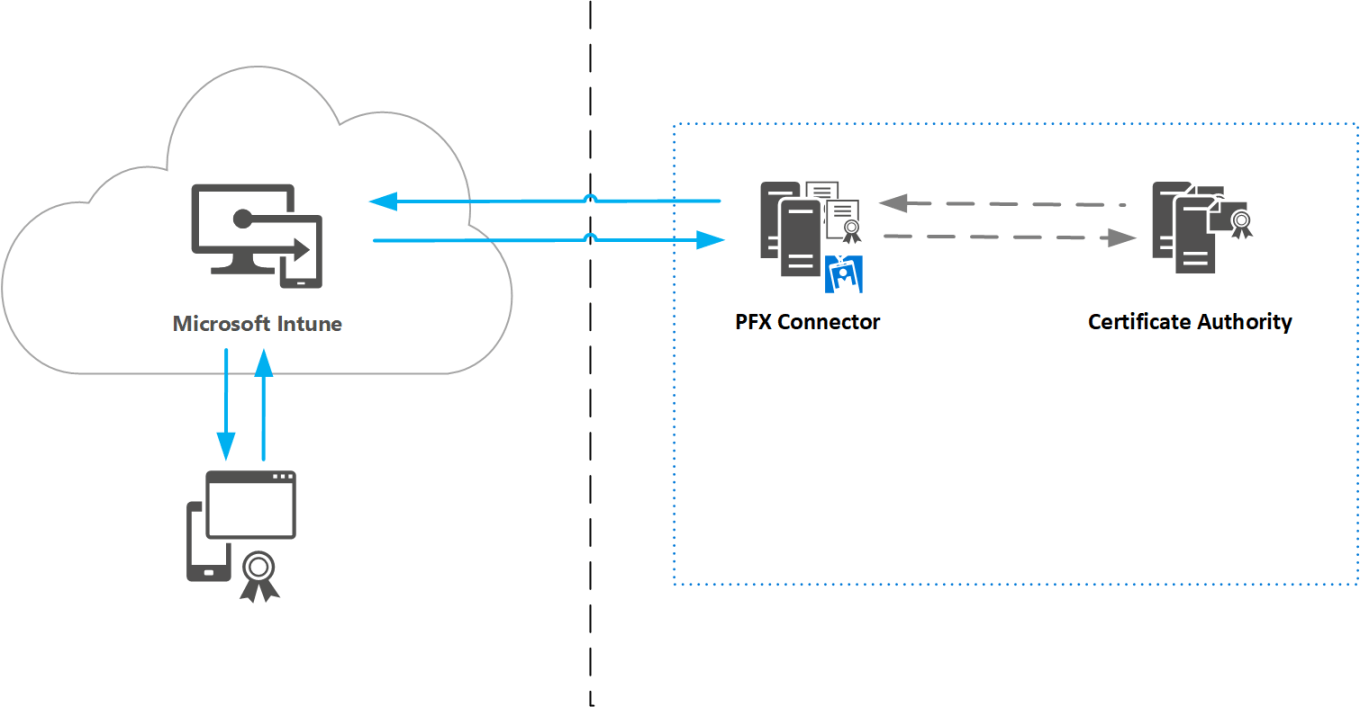
The process
Certificate traffic originates shortly after enrollment of a device as it will receive a certificate profile policy. Intune is aware of this enrollment and sends a certificate request to the PFX connector. The PFX connector will “forward” this request to the Issuing certificate authority (CA). The Issuing CA receives the request and will create a user certificate, based on a pre-configured certificate template. The CA will send the certificate to the PFX connector. The PFX connector sends the certificate to Intune. Intune ultimately sends the certificate to the device of the user that has started the enrollment.

- Intune administrator creates a PFX certificate profile and deploys it;
- Intune service sends a certificate request to the PFX connector;
- The PFX connector receives the PFX blob and send the certificate request including configuration to the on-perm CA;
- The CA issues an user certificate and sends it back to the PFX connector;
- The PFX connector sends the encrypted user certificate to the Intune service;
- Intune decrypts the PFX user certificate with KRA and re-encrypts the certificate using the device management certificate, then sends it to the device.
- The certificate status is reported back to the Intune service.
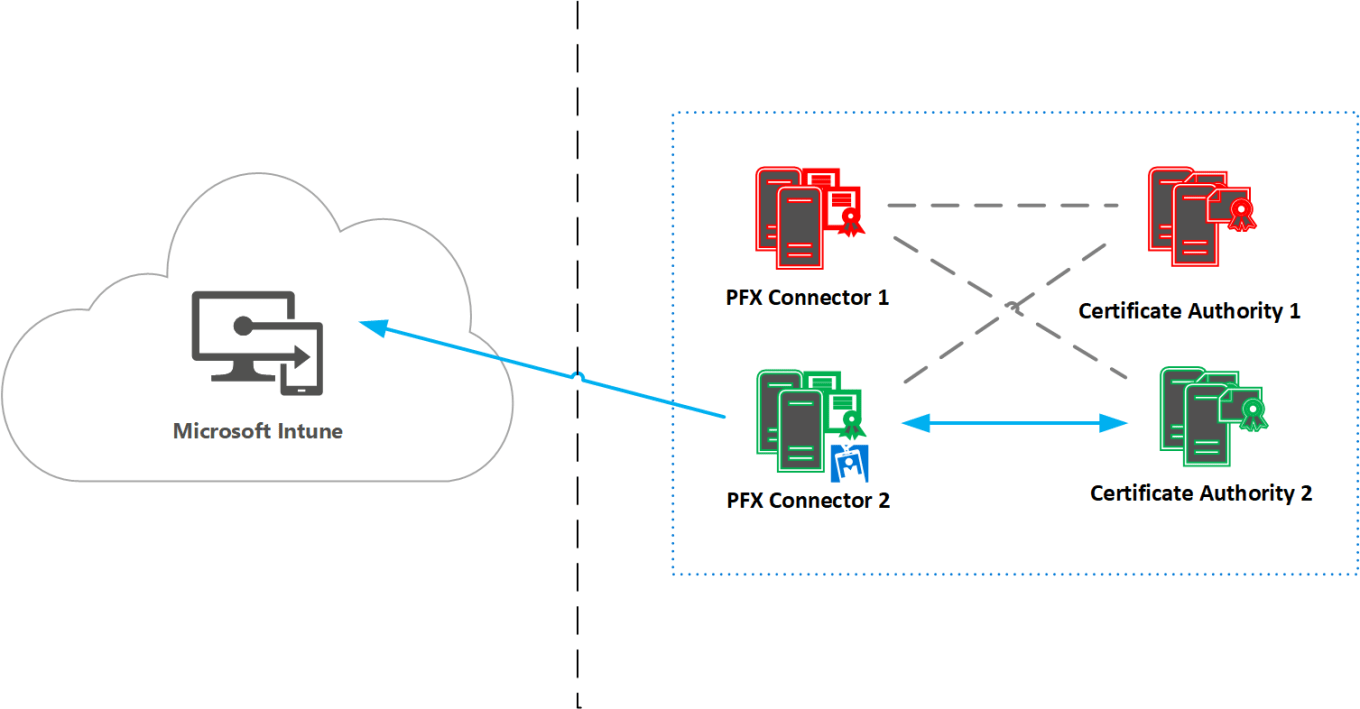
High Availability
Important subjects for an enterprise architecture are most often non-functional requirements. An enterprise architecture must provide a high available solution taking into account disaster recovery process/procedures. By design the PFX connector doesn’t provide support for high availability. The PFX connector is installed as an single instance with no option for multiple active PFX connectors. You can install multiple PFX connectors but there can only one active at the same time.
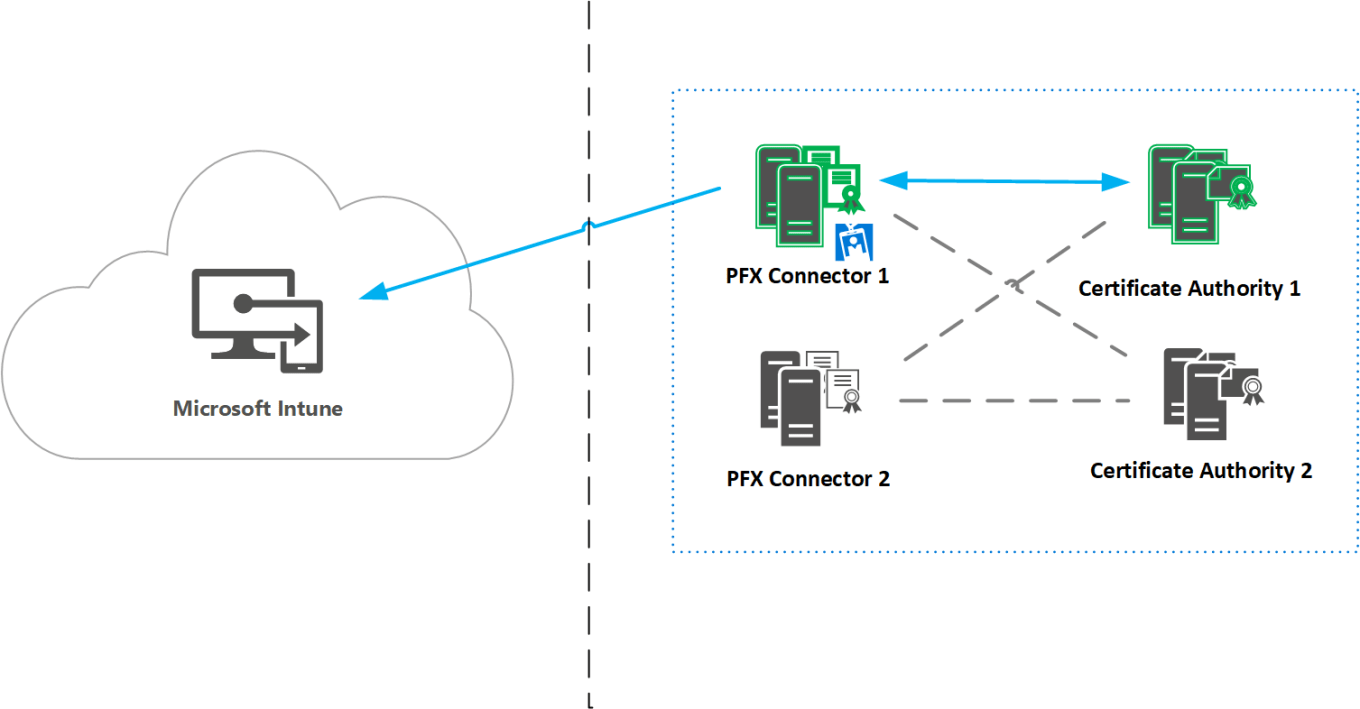
Multiple PFX connectors can be installed however only a single PFX connector can be actively registered to the Intune service to perform operational certificate tasks such as certificate requests, renewals or revocations. As the PFX connector is key component in this solution we required to provide a disaster recovery plan to minimize downtime in case of failure. Devices which contains a valid certificate are not directly effected as they’re still able to access corporate resources. Once a devices is retired/wiped we must be sure that the certificate is removed on the device, but more important the certificate is revoked on the CA.
Below some examples of disaster recovery scenarios whereby the second PFX connector is pre-installed on a 2nd server which is already pre-configured (prerequisites like firewall, connectivity, etc.).


Revocation
Besides issuing- and renewing certificates, the revocation process is the most critical process of certificate based authentication. In case when an user is leaving the organization or in occasion of a lost/stolen device, we must be sure that access to corporate resources is prohibited instantly.
The table below shows you an overview the action performed based on an event occurred. In a hybrid scenario the Certificate Registration Point (CRP) initiates the revocation whereby in a standalone scenario the PFX connector issues the revocation action.
| Event | Intune Standalone | Intune Hybrid |
| Retire (User initiated) | Certificate deleted & revoked | Certificate deleted & revoked |
| Retire (Admin initiated) | Certificate deleted & revoked | Certificate deleted & revoked |
| Block | N/A | Revoked |
| Delete | N/A | Certificate deleted & revoked |
| Leave group/collection | Certificate deleted & revoked | Certificate deleted & revoked |
| Delete SCEP/PFX profile | Certificate deleted & revoked | Certificate deleted & revoked |
| Remove targeting / deployment | Certificate deleted & revoked | Certificate deleted & revoked |
In my next blog of this series I’ll go into more details about where to start troubleshoot when you’re facing issues deploying certificates using Microsoft Intune PFX connector. We’ll drill down into the behavior and anatomy of the Microsoft Intune Connector.
In meantime stay productive and secure! :-)
Sources
- Configure certificate infrastructure (classic Intune portal)
https://docs.microsoft.com/en-us/intune/deploy-use/configure-certificate-infrastructure-for-pfx
- How to configure certificates in Microsoft Intune (new Intune Azure portal)
https://docs.microsoft.com/en-us/intune-azure/configure-devices/how-to-configure-certificates
- Configure your Microsoft Intune certificate infrastructure for PKCS (PFX)
- Configure certificate infrastructure for SCEP in Microsoft Intune
Categories
Thanks for a very good article. I have some questions that I hope you can (maybe) help with ?
a) If a user deletes their certificate – how can the same user get a new certificate ?
b) How is renewal of the certificates done (initiated by client or intune) ?
c) Can device certificates be deployed with PKCS to devices ?
d) It seems like there is one user certificate per device deployed – is this expected/correct ?
If YES – how can I in my on premise environment identify a specific certificate to a specific device ?
Hi Rikard, sorry for the delay but complements for the questions. I like these kind of questions!
a) Not sure if a user is able to delete the cert. This wouldn’t be detected, certificate got (re)deployed on configured renewal interval. Re-enrollment triggers cert deployment. Use supervise mode to prohibit
b) Yes, this is service initiated not client initiated.
c) In theory this might be possible, which might manual steps to perform. What is the use-case for device certificates? Multi-user scenarios?
d) Yes, there is one user certificate deployed per device. However, per feature configured a copy will be displayed (VPN + User = 2 certs. VPN + User + E-mail = 3 certs. The service is taking care of the of the cert, user & device mapping. I believe the device Id’s are in the subject or cert properties. I’ve to sort this out to be sure, so I’ll get back to you when checked.
Hi,
This article is very good !
and I have a one question.
Is Intune Certificate Connector compatible with products other than Symantec?
As far as reading the document, it seems to be compatible with Symantec only.
Hi Nameko, glad it was usefull. No currently only support for native Microsoft & Symantec CA. https://docs.microsoft.com/en-us/intune/certificates-symantec-configure
Hi Ronny,
I’m in the process of trying out the PFX connector for Intune and found your blog, which has been a real help to understand the product! One thing I have a hard time understanding is the full traffic flow and MS documentation doesn’t bring much light on this either. Do I have have to allow incoming TCP\443 to the server hosting the PFX Connector or is the PFX Connector initiating the connection to Intune? If it’s the prior, do I need a public SSL certificate installed on the PFX Connector?
Thanks again for a great blog!
Best regards,
Rob
Hi Rob,
I’m glad to hear it was useful for you. Good question! The PFX Connector is based on a Microsoft connector framework which is commonly used for for other Microsoft services like Azure AD Connect (Health Agent) or Azure AD Application Proxy. The characteristics (and huge benefit) of this framework it’s outbound initiated which doesn’t requires any inbound traffic and thus no actions required for opening/publishing ports. Just outbound internet access (preferably no proxy) will do the trick.
Best, Ronny
Clear as day! Thank you!
Hi there,
I’ve been trying to setup the connector on a Wins Svr 2016 and seem to be stuck with this error below
Enrollment Failed. Error: System.Net.Http.HttpRequestException: An error occurred while sending the request. —> System.Net.WebException: The underlying connection was closed: An unexpected error occurred on a receive. —> System.IO.IOException: The decryption operation failed, see inner exception. —> System.ComponentModel.Win32Exception: The message received was unexpected or badly formatted
Any ideas would be very helpful