In a diptych I’m sharing my experiences, common practices and challenges of implementing Microsoft Intune PFX connector as certificate deployment mechanism in the enterprise.
In my first blog post I covered the basics of implementing a certificate deployment infrastructure based on Microsoft Intune PFX connector. Explained the differences and considerations whether to choose SCEP or PFX as your certificate deployment solution. And explained the certificate issuing workflow. In this second post I’ll go in more detail of the anatomy of the Intune Certificate Connector, setup. Explaining the renewal and revocation process(flow) works. And lastly I give you some pointers where to start your journey, in case of troubleshooting certificate deployment issues.
Part 1 – Deploying Microsoft Intune Connector in an Enterprise world: common practices
Part 2 – Deploying Microsoft Intune Connector in an Enterprise world: troubleshooting
Anatomy
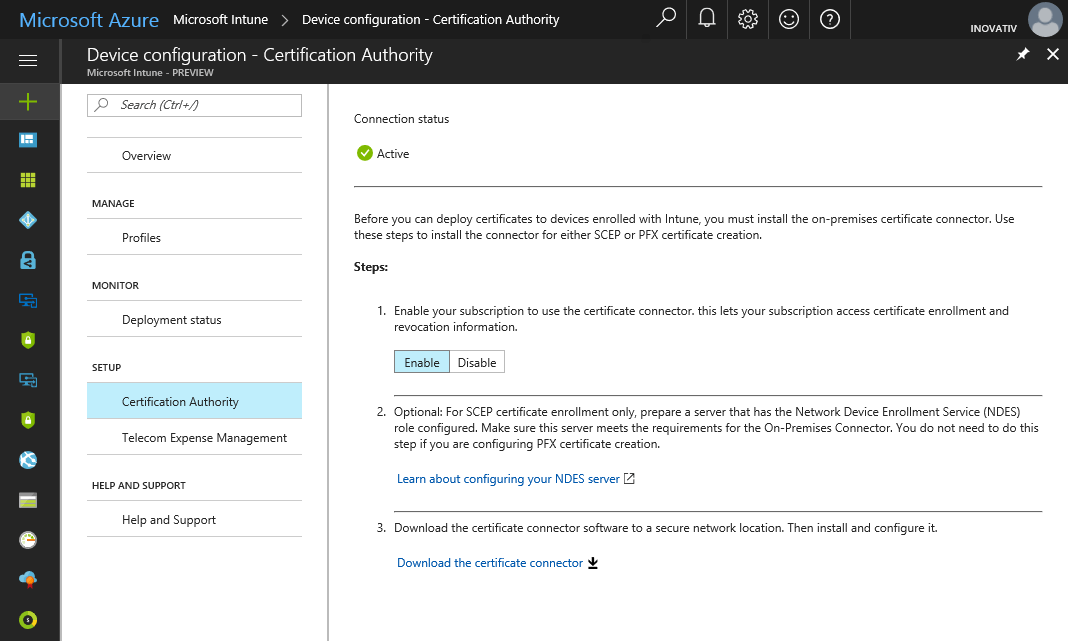
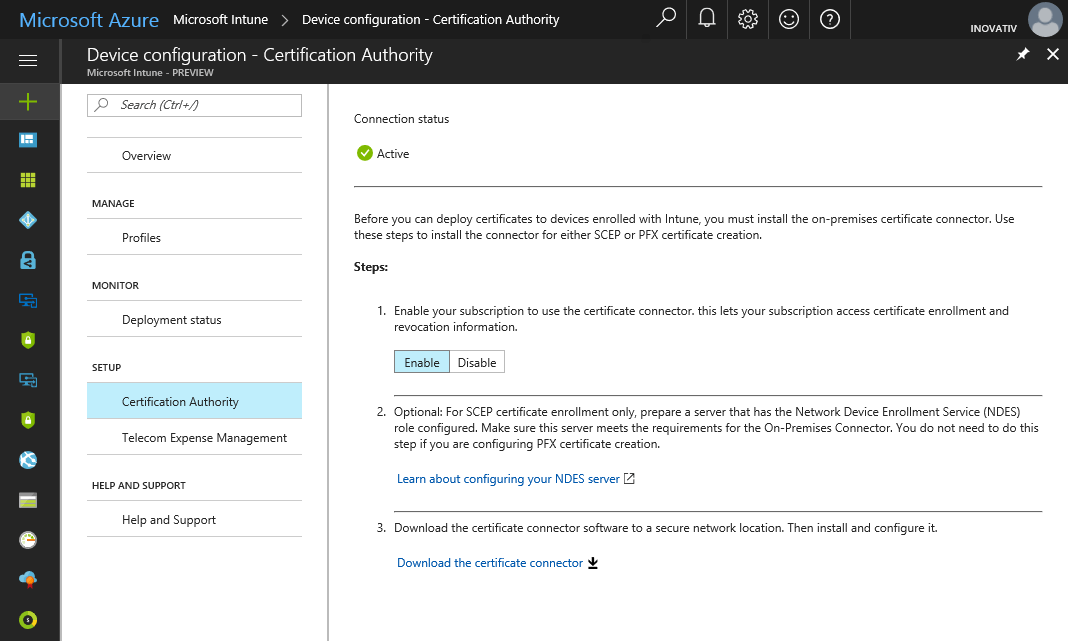
The Intune Certificate Connector forms the connection between your on-premise certificate (CA) infrastructure and Microsoft Intune cloud services in order to issue certificates to you managed endpoints. The Intune Certificate Connector can be downloaded once you enabled the Certificate Connector in your Intune subscription.
During the setup of the Intune Certificate Connector you’ve the option to configure SCEP and PFX of PFX only.

Service Account
By default the Windows service of the Intune Certificate Connector runs under the computer account security context of where the Intune Certificate Connector is installed on. Make sure when specified a service account, it has Issue and Manage Certificates permission on your issuing Certificate Authority (specifying a service account is optional).

Once you installed and successfully registered the Intune Certificate Connector the connection status appears Active in you Intune subscription. From here you’ll deploy a trusted root and intermediate (if applicable) followed by a PFX certificate profile. In the table below all components shown of which the Intune Certificate Connector consists of.
|
Value |
| Binaries
Location where all components of the Intune Certificate Connector are located.
|
C:\Program Files\Microsoft Intune

|
| Interface
This is the folder location where the Intune Service Connector UI, configuration and log file are located.
|
C:\Program Files\Microsoft Intune\NDESConnectorUI

|
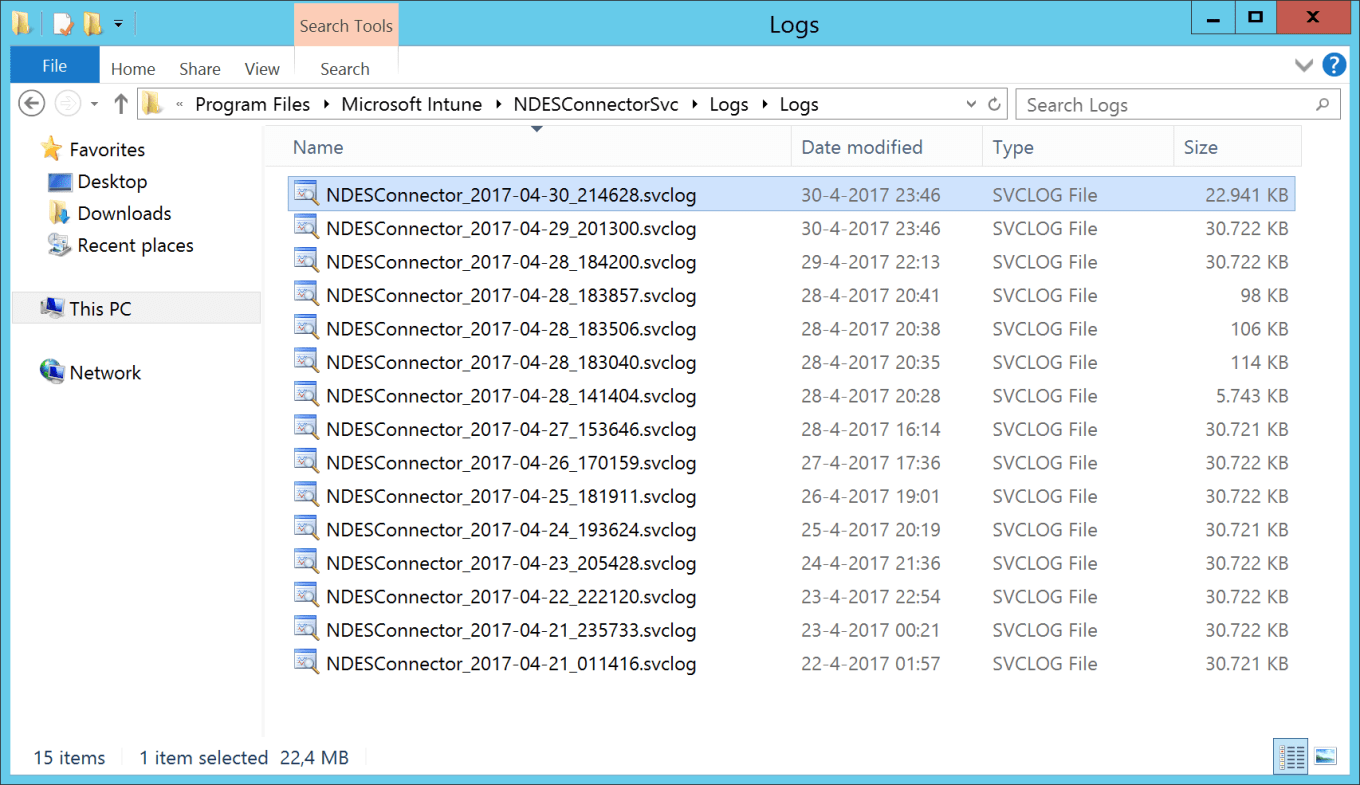
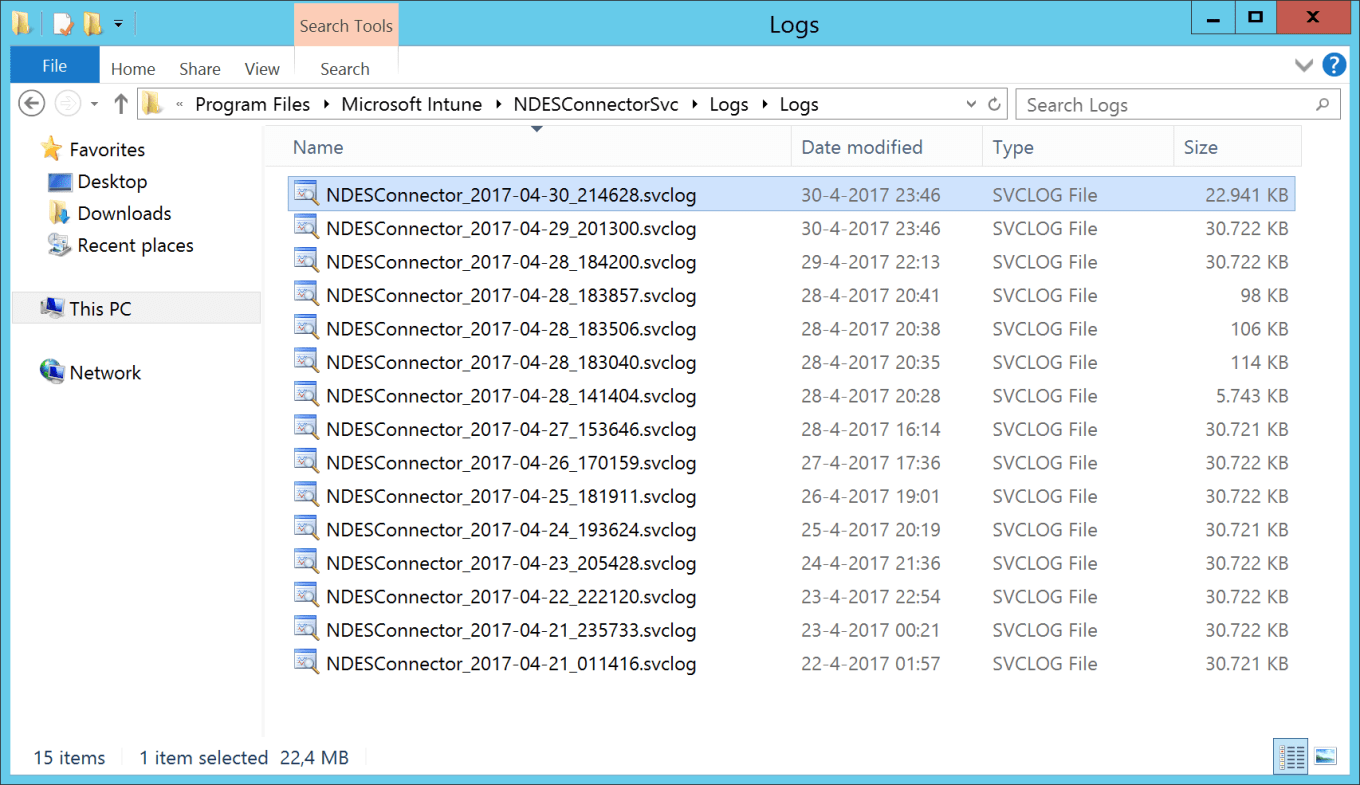
| Log Files
This is the location where the Intune Connector Services stores it’s log files, including certificate request, renewal or revocation.
|
C:\Program Files\Microsoft Intune\NDESConnectorSVC\Logs\Logs
|
| Registry |
HKLM\Software\Microsoft\MicrosoftIntune

|
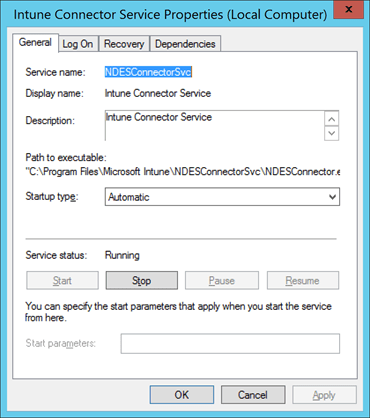
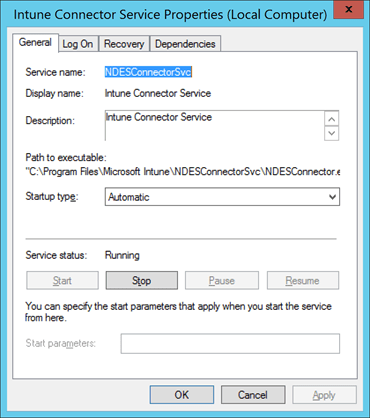
| Windows Services
This is the folder location where the Intune Service Connector services and configuration file are located.
|
Intune Connector Service
C:\Program Files\Microsoft Intune\NDESConnectorSvc\NDESConnector.exe
|
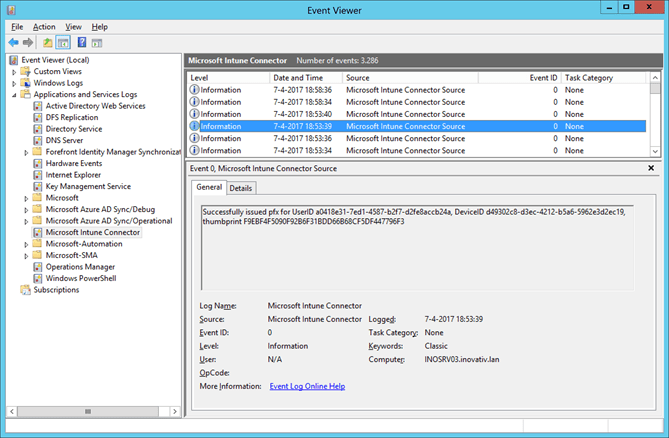
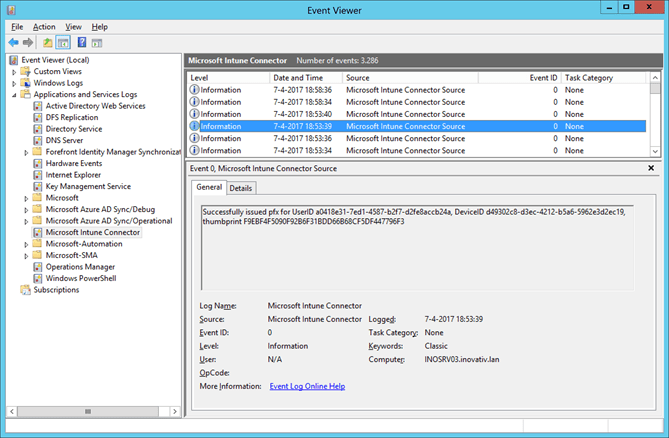
| Event Viewer |
Application and Services Logs\Microsoft Intune Connector
|
Troubleshooting
Troubleshooting Intune Certificate Connector can be challenging. Understanding the process and autonomy gives you a good starting point to successfully determine the issue or even solve your problem. In the table below most common steps involved are listed in chronological order.
|
Components |
|
What |
Location |
| 1. |
Intune Connector |
Services |
Make sure the Intune Connector services is running |
C:\Windows\System32\services.msc |
| 2. |
Intune Connector |
Event viewer |
Make sure no errors/warnings events reported |
Application and Services Logs\Microsoft Intune Connector |
| 3. |
Intune Connector |
Connectivity/ Network |
Make sure Intune Connector connection state has no issues |
C:\Program Files\Microsoft Intune\NDESConnectorUI |
| 4. |
Intune Connector |
Log files |
Make sure no errors reported in Intune Connector transaction log file(s) |
C:\Program Files\Microsoft Intune\NDESConnectorSvc\Logs\Logs |
| 5. |
Intune Connector |
Log files |
Make sure no errors reported in Intune Connector UI log file |
C:\Program Files\Microsoft Intune\NDESConnectorUI\Logs |
| 6. |
Certificate Authority |
Certificate Services |
Make sure the computer account of the Intune Connector has granted access to your CA(s) |
C:\Windows\System32\certsrv.msc |
| 7. |
Certificate Authority |
Certificate Services |
Make sure the service account of the Intune Connector has granted access to the certificate template |
C:\Windows\System32\certsrv.msc |
| 8. |
Certificate Authority |
Event viewer |
Make sure no errors/warnings events reported |
Application and Services Logs\Certificate Services |
| 9. |
Intune Connector |
Processing |
Make sure no PFX requests files (PFR) are in Failed PFXRequest folder |
C:\Program Files\Microsoft Intune\PfxRequest\Failed |
| 10. |
Intune Connector |
Processing |
Make sure no PFX requests files (PFR) are queued in Processing PFXRequest folder, the PFX requests files (PFR) size are 2KB |
C:\Program Files\Microsoft Intune\PfxRequest\Processing |
| 11. |
Intune Connector |
Successful |
Make sure PFX requests files (PFR) size is 7KB or larger |
C:\Program Files\Microsoft Intune\PfxRequest\Successful |
| 12. |
|
|
Contact Microsoft Intune support |
|
WCF Trace Viewer
The log files of the Intune Certificate Connector are generated in a *.svclog file extension. Best way to analyze these log files in a readable format is Windows Trace viewer. Windows Communication Foundation (WCF) Service Trace Viewer Tool helps you analyze diagnostic traces that are generated by WCF. Service Trace Viewer provides a way to easily merge, view, and filter trace messages in the log so that you can diagnose, repair, and verify WCF service issues.

https://msdn.microsoft.com/en-us/library/ms732023(v=vs.110).aspx
Miscellaneous
The Intune Certificate Connector is frequently updated and includes often fixes or (service) improvements. Unfortunately both Silverlight- and new Azure Intune portal doesn’t provide insights (yet) whether you’ve installed the latest version of the connector.
When you’re planning to update the connector than it’s good to know there is no impact other than the Intune Certificate Connector services will be restarted during the upgrade. There is no need to provide your Intune Service admin or Global admin credentials. The service credentials (certificate) remains preserved.
In case you’ve to re-register the Intune Certificate Connector you must delete SC_Online_Issuing certificate(s) (Local Computer)\Personal\Certificates) prior to re-register the Intune Certificate Connector. Re-registering might be required as part of a fallback scenario as described in my first blog. Re-registering doesn’t require you to reinstall the Intune Certificate Connector. The re-registration is initiated by starting the Intune Certificate Connector UI.
Advanced Troubleshooting
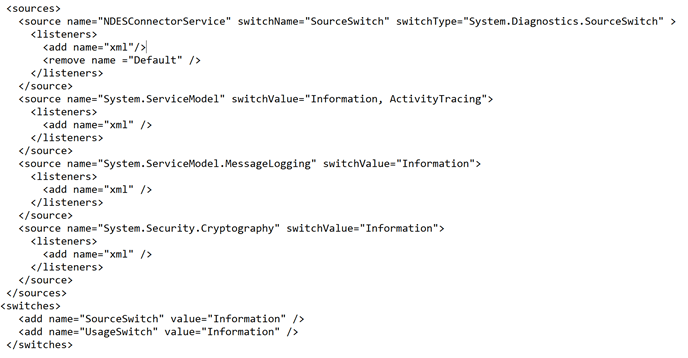
When the default log files are insufficient, the log level (debug/verbose) can be configured by adjusting the NDESConnector.exe.config. Besides log levels, we can adjusts the TimeFrequency, PFXTimeFrequency and IntuneServiceTimeout.
Important!
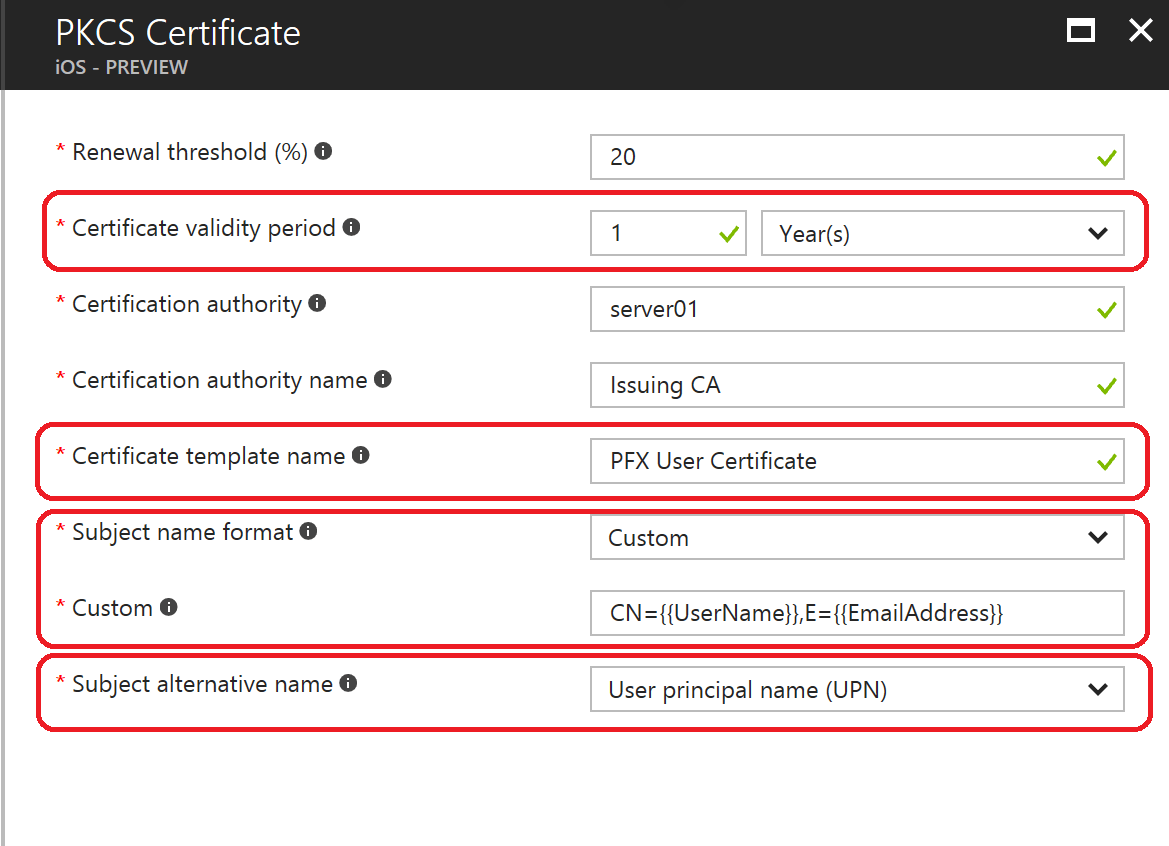
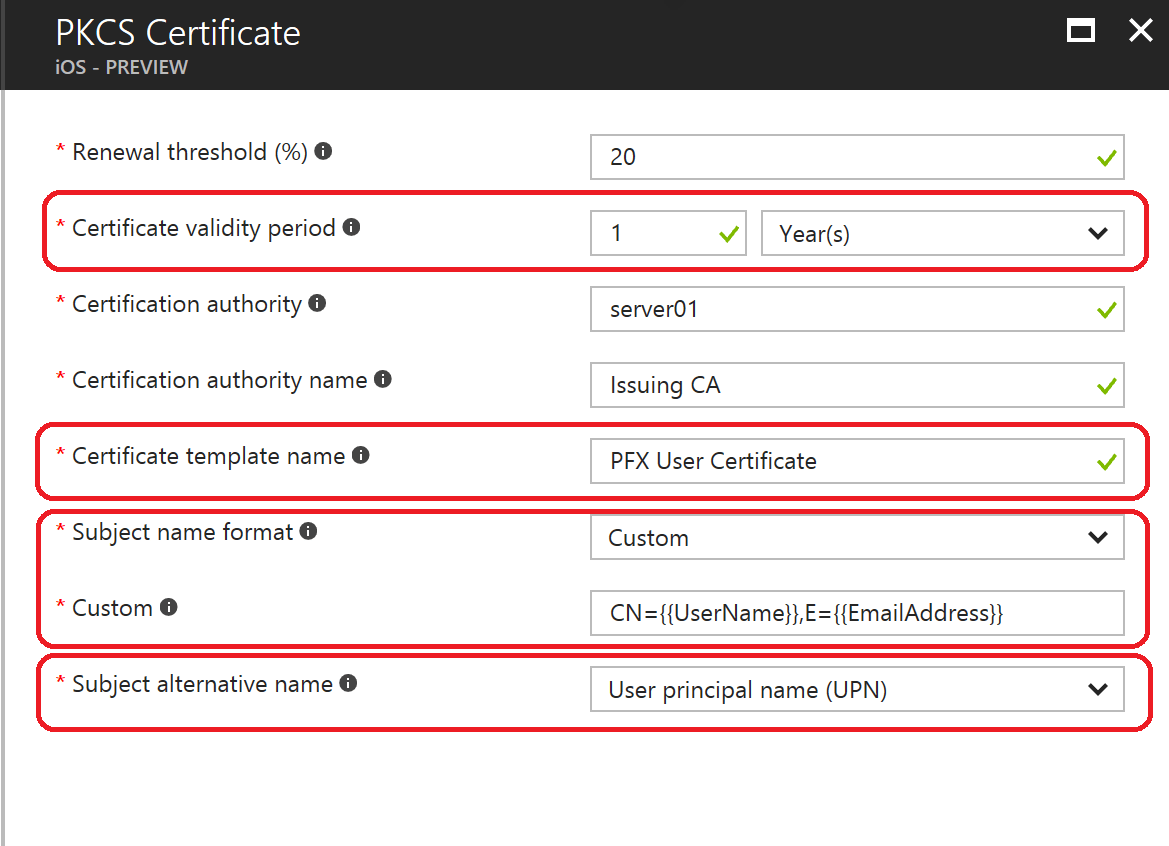
Be reluctant on changing your certificate parameters in your certificate policies. Changing one of these parameters will cause reissuing of all certificates! This impacts the user(s) of which the certificate policy were targeted to.
Certificate Template Parameters:
-
- KSPSetting
- CertificateStoreLocation
- TemplateName
- SubjectNameFormat
- SubjectAlternativeNameFormat
- CertificateValidityPeriod
|
 |
Sources







What do you mean on step 11? Mine are 2k. Where did you get the information that it should be larger than 7kb?
When the cert request is in process it should be 2kb large, but when successfully processed the file should be 7kb large as it contains the blob file. Based on your feedback I’ve updated the blog post. Once again appreciated your feedback!
That is good to know. I’m having issues where they are processing, but never successful. Keep getting IssuePfx -Generic Exception: System.ArgumentException: CCertRequest::Submit: The parameter is incorrect. 0x80070057 (WIN32: 87 ERROR_INVALID_PARAMETER)
Any ideas? I’ve searched all over the net.
Is your CA reachable from the server where your connector is installed on? Did you checked your CA eventlog? If possible, can you send me the connector logfiles?
Hi Eli,
were you able to solve the issue? i`m having exact the same bahaviour.
best regards
If you can share me the logfiles and the configuration of the PFX profile?
Hi Ronny,
we found the issue. It was the friendly Name of the CA in the Intune PKCS Profile. After changing the CA friendly name in the Intune profile the profile still sent the old (wrong) Name in the request.
Workaround: Delete the PKCS profile in Intune and generate a new one. After this the correct CA friendly name was sent in the request.
best regards
Good to hear it’s solved and appreciated to circle this back!
Thanks for the article, really useful.
I had the same issue when deploying to iOS devices but in my case it was down to the CA Name. The tool tip asks for the FQDN of the CA, but this didn’t work. When I recreated the name with just the NetBIOS name it worked straight away.
Oh well, may come in useful for someone else experiencing the same issue.
Hello Ronny,
Trying to implement SCEP with Intune Connector.
Trusted Certificate Profile distributes perfectly with status “Succeed” but SCEP Certificate recieves “Error”. I’ve tried to read all logs I can find but I’m stuck.
How can i expand this “Error” in Intune to see what’s really wrong?
Intune Connector communicates OK.
IIS Recieves the request.
Then the thread is lost.
Hi Ronny
I have NDES setup with intune connector for mobile devices. Currently, my on-premises NDES setup is working fine. Down the line, if I need to renew my connector certificate which is in NDES server, Do we need to reinstall the connector or we can just change the thumbprint by placing new certificate in personal store as mentioned in below link.
Kindly advice. Thanks!!
https://support.microsoft.com/en-in/help/4045957/you-can-t-issue-scep-certificates-to-devices-in-intune-after-a-certifi
Yes, please follow the procedure as described in the support article. I wouldn’t reinstall the connector if necessary. It can be considered as last resort as it’s straightforward process. Alongside you might consider a second SCEP connector as well. This as it provides a side by side fix and provides high availability.
Thanks and sorry for the delayed reply. As you said it worked for me without reinstalling the agent
Hello Ronny , Please suggest the communication port being used for PKCS integration of Intune with NDES connector , For inbound Traffic when Intune request Certficate to NDES is that Traffic is Encrypted and Cause any Security concern .
Hi, the benefit of using the Intune Certificate connector (NDES/PFX) it doesn’t require inbound ports as it’s outbound initiated. Your only “concern” here is that outbound traffic (80/443) is allowed from your connector to Microsoft services.
Thanks Ronny , My concern is for inbound request when Intune request to NDES server for certificate ( inbound traffic from cloud to NDES server ) is that not generate inbound traffic to NDES server and organization network, Security folks are concern . May be I am missing something.
There is no inbound traffic as the connector is polling (outbound initiated) the Intune service on a schedule. From connector to internal CA you’re using RPC. See https://ronnydejong.com/2017/02/20/part-1-deploying-microsoft-intune-pfx-connector-in-an-enterprise-worldcommon-practices/ for the networkflow of Intune connector.
Hi Ronny,
Thank you for the great document. I see you have mentioned inbound is not required for NDES PFX connector. We are planning to provision device over internet (Windows Autopilot) and distribute certs while provisioning. I see here – https://oofhours.com/2020/04/05/intune-certificates-something-everyone-should-set-up/ (written for SCEP) that NDES should be in internet. Is this not applicable for PKCS/PFX connector? I am asking this because of the use case is internet and i am assuming SCEP and PKCS both uses NDES?
Thanks you again,
Saravanan R
Hi Ronny,
Thank you for the great document. I see you have mentioned inbound is not required for NDES PFX connector. We are planning to provision device over internet (Windows Autopilot) and distribute certs while provisioning. I see here – https://oofhours.com/2020/04/05/intune-certificates-something-everyone-should-set-up/ (written for SCEP) that NDES should be in internet or connected through reverse proxy. Is this not applicable for PKCS/PFX connector? I am asking this because of the use case is internet and i am assuming SCEP and PKCS both uses NDES?
Thanks you again,
Saravanan R
Hi Saravanan, I’m glad to hear! In short NDES/SCEP is internet facing whereby the URL of your NDES is published to the internet. As mentioned in the article, this is easily done by using Azure AD Application Proxy. PKCS/PFX certificate request goes through the Intune service, which is connected to your on-premise by using the PFX connector. The PFX connector requires only an outbound connection to the internet, it works the same as other Microsoft connectors such as Azur AD Connect).
Hi Ronny; Great information here. Can you tell me how to increase the amount of time the svc logs persist? I am only seeing one day’s logs at a time and I need more. I have checked the registry setting, config file, these documents, Microsoft documents and Tech Community, I just cannot find anything.
Thanks for dropping a line! Please check the NDESConnector.exe.config located in “.\Program Files\Microsoft Intune\NDESConnectorSvc” folder. In the “appSettings” section you can tweak a few parameter (TimerFrequency, PFXTimerFrequency) which affects the retention of the logfiles. In addition you can tweak the logfile size by adjusting the logging parameter via the following registry hive “HKLM\Software\Microsoft\Jupiter\Logging”
Disclaimer! Please take into account changing the default values might negatively impact the services and might put you in an unsupported state.
Hi spencer
I had the the issue and deleting and re-creating VPN profile did solve. Thank you for sharing
Good afternoon, we are looking to deploy this in our environment. But there are questions around the architecture and security. Would it be possible to contact you directly to ask more specific questions? Our focus is Morton in IOS/ Android deployments
Hi Jessy, please feel free to reach out via ronny.de.jong@outlook.com Regards, Ronny