Microsoft Defender ATP’s diary: From a SecAdmin’s Perspective
This blog post is an introduction of a series of blogs to cover the game changing risk-based approach Microsoft Defender ATP offers to the discovery, prioritization, and remediation of endpoint vulnerabilities and misconfigurations.

As mentioned in “The evolution of Microsoft Threat Protection” by Debraj Ghosh, PM of Microsoft Threat Protection, security comes
in general with two responsibilities: 1) Security Operations (SecOps) and 2) Security Administrations (SecAdmins).
SecOps act by incident response via a centralized alert view and powerful hunting capabilities enabling ad-hoc investigations.
SecAdmins will gain the visibility, control, and guidance necessary to understand and act on the threats currently impacting their organization, as well as information on past and future threats.
In this series of blogs I will focus exclusively on the responsibility of a SecAdmin and all aspects that Microsoft Defender ATP has to offer in regards. Therefore we kick off this serie starting with Configuration Management and Threat & Vulnerability Management.
Configuration Management

Configuration Management is another new kid of Microsoft Defender ATP. It helps you to ensure that every endpoint in your environment is managed. Configuration Management provides both security administrators and security operations teams with unique value, including:
- Onboarding of Intune-managed Windows 10 devices to Microsoft Defender ATP.
- Deployment of Microsoft Defender ATP Security baseline(s) to Intune-managed Windows 10 devices.
- Management of machine attack surface rules for predictive analysis and tuning of attack surfaces to Intune-managed Windows 10 devices.
Threat & Vulnerability Management
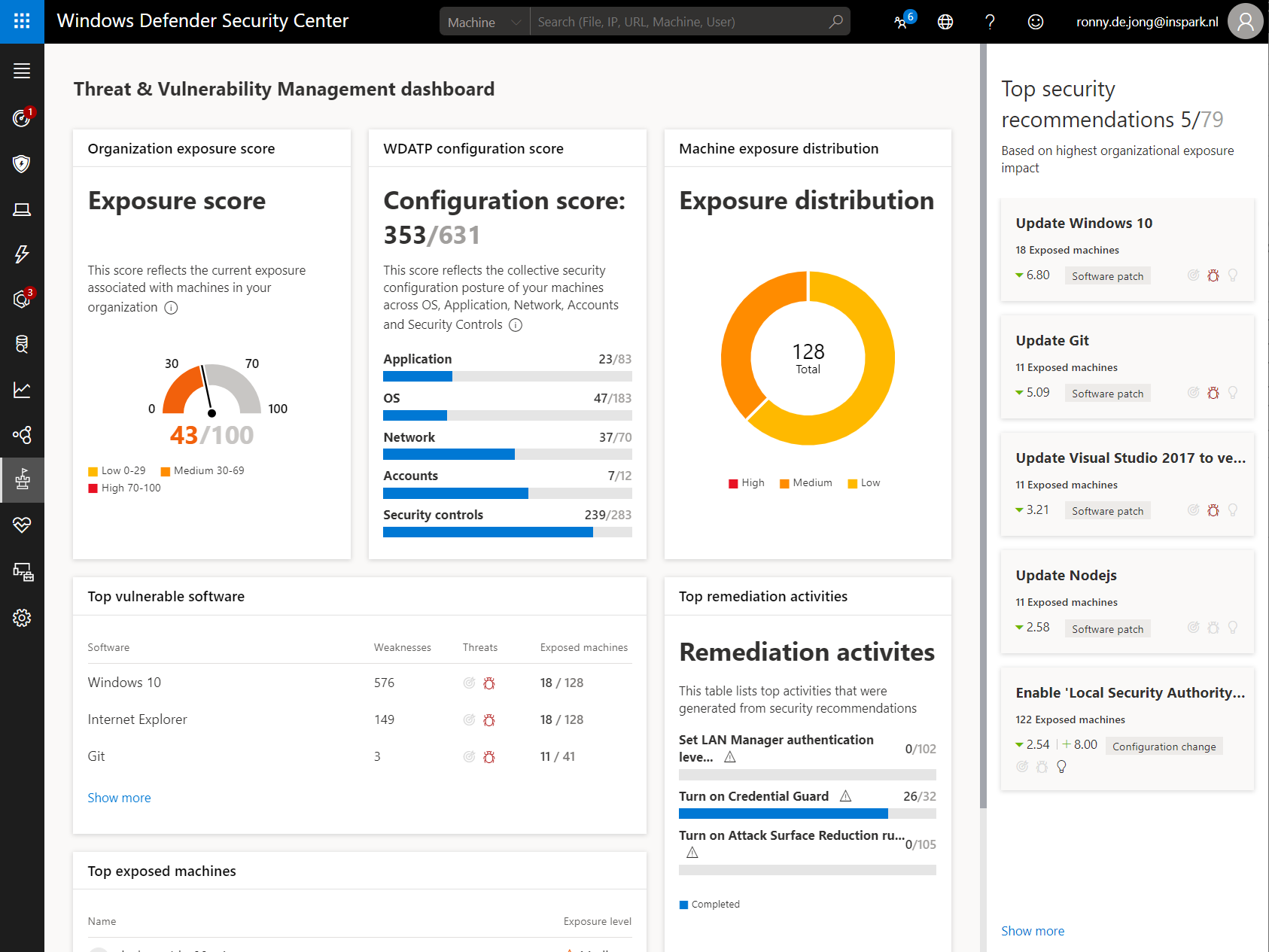
Threat & Vulnerability Management is a new Microsoft Defender ATP component that helps effectively identify, assess, and remediate endpoint weaknesses. Threat & Vulnerability Management provides both security administrators and security operations teams with unique value, including:
- Real-time endpoint detection and response (EDR) insights correlated with endpoint vulnerabilities
- Invaluable machine vulnerability context during incident investigations
- Built-in remediation processes through Microsoft Intune and Microsoft System Center Configuration Manager
The outline...
As mentioned I’ll elaborate in a number of blog post all the aspects starting from on-boarding your endpoints to what it takes to get in control and more important to stay in control.
- Fix the basics: Make sure rogue endpoints have no right to exist.
- Get secure, stay secure: Security baselines are your best friend.
- Threat resilience are the new norm: Reduce your vulnerable footprint before even threats being able to harm you.
- Improve your endpoint security posture: Raise the bar, measure up to the ‘golden’ standards.
- Automation as recipe for success: Automated remediation as the engine to get in control and stay in control.
What can you expect? I’ll explain which on-boarding options exists and how to on-board your endpoints following common-practices. We’ll consider the power of security baselines and how to implement them via Microsoft Intune (integration). Via Threat & Vulnerability Management you’ll discover vulnerabilities of your endpoints and how to mitigate them…preferably automated again, with the integration of Microsoft Intune or System Center Configuration Manager (SCCM).
By raising the security bar we’ll determine our starting point using Secure Score. These valuable insights will help us to make the right decisions and make the difference, based on priorities and impact. At last there are so many moving parts to keep up with (mis)configurations, (software) vulnerabilities & weaknesses. Therefore automation is indispensable to both security administrators and security operations teams.
Looking forward assuming you’re compro…eh assume you stay tuned! ;-)
Categories
One thought on “Microsoft Defender ATP’s diary: From a SecAdmin’s Perspective” Leave a comment ›